Basic Policy
We at the Shimadzu Group shall obtain, safely handle, and dispose of any confidential information or personal data relating to our company or its subsidiaries' customers, employees, business partners and their personnel, and shareholders and investors in accordance with applicable rules and laws.
General Principles

(1) Building, Promoting, and Improving the Information Security Structure
Shimadzu shall establish an information security committee. The committee shall share the content and purpose of measures across the entire group and promote their implementation. In addition, we shall continuously improve the structure.

(2) Obtaining Information in an Open and Fair Manner
We shall not obtain confidential or personal data using unethical means.

(3) Obtaining, Using, Managing, and Disposing of Information Appropriately
We shall obtain, use, manage, and dispose of information or data about business processes and technology received from customers, suppliers, or job applicants, and internal information or data about Shimadzu business processes or technology, appropriately in accordance with all applicable laws, regulations, contracts, and internal company rules.

(4) Defending Against Cyber-Attacks
We shall implement technical, physical, and human measures to prepare for cyber-attacks, increase the level of protection, and respond quickly to security threats.
Efforts
Improving Information Security Within the Shimadzu Group
Shimadzu Group will continue to promote the enhancement of information security to manage confidential information and personal data related to our company or our subsidiaries, customers, employees, partner companies and their representatives, and shareholders/investors based on appropriate rules and laws, in order to prevent fraud and misuse.
Management Structure for Information Security
The Shimadzu Group periodically conducts Information Security Committee meetings, chaired by the director in charge of DX and IT strategy department, and has established systems for deploying committee decisions throughout Shimadzu Corporation and Group companies.
The committee discusses the direction and content of initiatives, formulates related regulations incorporating human, organizational, and technical measures, decides on the introduction of new management strategies and tools, and manages, promotes, and improves information security, including the handling of personal data.
In addition, the committee has been establishing communication networks with domestic and international subsidiaries to facilitate information sharing, the formulation of new policies, and the development of emergency response procedures to minimize damage in the event of an information security incident.
The organizational structure in Japan is as follows. Similar networks are being established in each region.
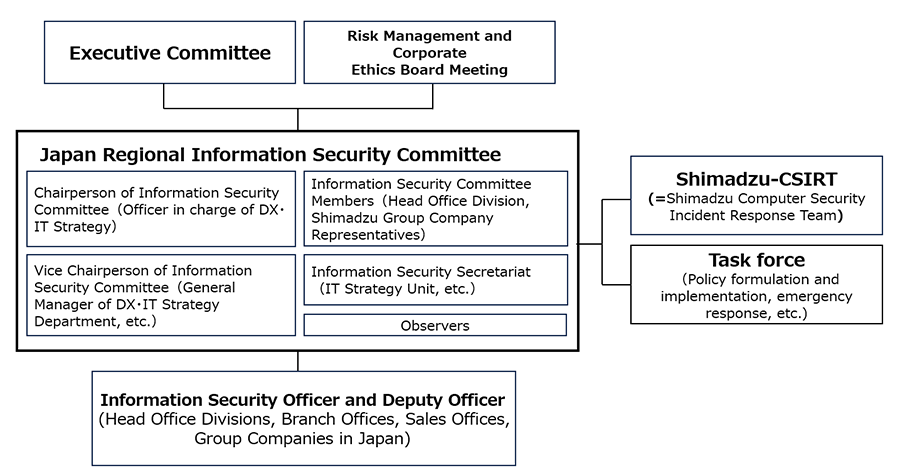
Incident Response
In the event of an information security incident, the Information Security Office and Shimadzu-CSIRT responds in accordance with the incident response criteria. If the incident is deemed to be of a high level, a countermeasures task force will be established to ensure rapid recovery and prevent recurrence.
Educational Measures for Information Security
The Shimadzu Group distributes the ‘Information Security Guidelines,’ which summarizes information security rules, conducts regular e-learning-based information security education, and conducts training on how to respond to suspicious and fraudulent emails to raise awareness of the importance of information security among all employees, and is committed to ongoing education.
- * Examples of e-learning content:
Information Security Measures, Personal Data Protection, Reporting Security Incidents, Publication on Prohibited Actions, Awareness Raising and Continuous Improvement Efforts, etc.
the Information Security Guidelines
Technical Measures for Information Security
To prevent information leaks and disruptions to business operations caused by cyberattacks, the Shimadzu Group implements malware countermeasures for networks and PCs, conducts vulnerability assessments and responses for public servers, and continuously collects and shares vulnerability and security information to mitigate the risk of security incidents.
Acquisition of Certifications related to Information Security
Shimadzu Business Systems Co., Ltd., a group company responsible for system development, has obtained the JIS Q 27001 (ISO/IEC 27001) information security certification. The company is committed to appropriately managing and effectively utilizing information assets.